I’ve learned recently that the iOS 11 camera app will now automatically scan QR codes and interpret them.
This is pretty cool, until now you needed special apps to do that for you on iOS.
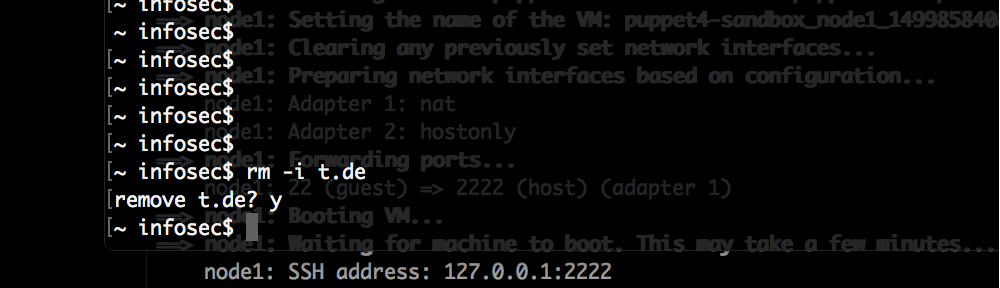
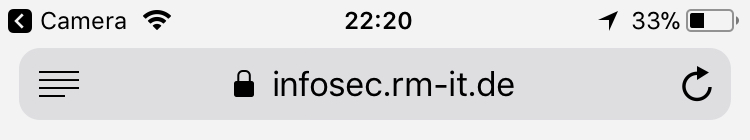
When scanning a QR code which contains a URL – in this case https://infosec.rm-it.de/ – iOS will show a notification like this:
Naturally the first thing I want to try is to construct a QR code which will show an unsuspicious hostname in the notification but then open another URL in Safari.
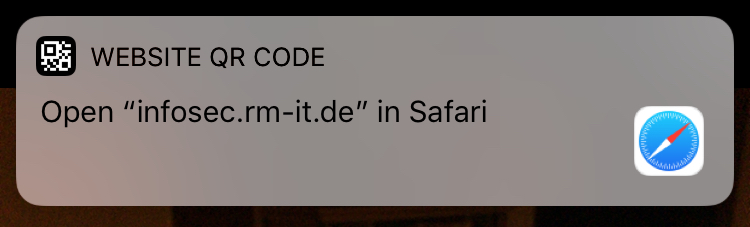
And this is exactly what I found after a few minutes. Here it is in action:
There is no redirect misuse being done on facebook.com, Safari will only access infosec.rm-it.de.
Details:
If you scan this QR code with the iOS (11.2.1) camera app:
The URL embedded in the QR code is:
https://xxx\@facebook.com:443@infosec.rm-it.de/
It will show this notification:
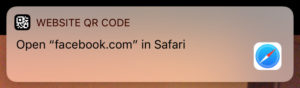
But if you tap it to open the site, it will instead open https://infosec.rm-it.de/:
The URL parser of the camera app has a problem here detecting the hostname in this URL in the same way as Safari does.
It probably detects “xxx\” as the username to be sent to “facebook.com:443”.
While Safari might take the complete string “xxx\@facebook.com” as a username and “443” as the password to be sent to infosec.rm-it.de.
This leads to a different hostname being displayed in the notification compared to what actually is opened in Safari.
This issue has been reported to the Apple security team on 2017-12-23.
As of today (2018-03-24) this is still not fixed.
Update:
On 2018-04-24 this has been fixed with iOS 11.3.1 and macOS 10.13.4.
CVE-2018-4187 has been assigned to both issues.